 Microsoft’s most recent addition to the Windows family of operating systems, Windows 10, is full of new features, but when it comes to implementing it, many businesses are still dragging their heels. However, the primary reason for this seems to be the fact that organizations want to make sure Windows 10 won’t break their IT infrastructure. Despite this handicap, Windows 10 is still being tested on twice as many PCs as Windows 8 was following its release.
Microsoft’s most recent addition to the Windows family of operating systems, Windows 10, is full of new features, but when it comes to implementing it, many businesses are still dragging their heels. However, the primary reason for this seems to be the fact that organizations want to make sure Windows 10 won’t break their IT infrastructure. Despite this handicap, Windows 10 is still being tested on twice as many PCs as Windows 8 was following its release.
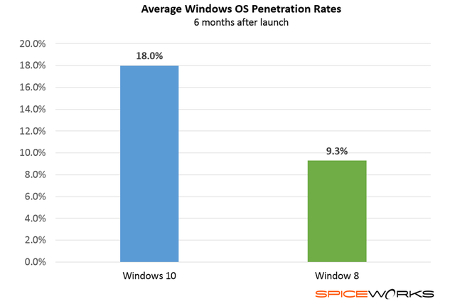
According to Spiceworks, 18 percent of businesses are testing Windows 10 for use with their organization, while only 9.3 percent of businesses were testing Windows 8 when it was released. What does this mean for Windows 10? For one, it shows that there’s much more interest in the OS than there was for Windows 8. This is important for Microsoft, especially due to the disappointing sales figures seen with Windows 8. Microsoft needed a way to get back in the game, and it seems Windows 10 was right on the money, as 94 percent of IT executives have expressed interest in Windows 10, so it’s just a matter of making sure that it works properly with mission-critical technology.
Why is Windows 10 being tested by so many more businesses than Windows 8 was? According to Spiceworks, it’s several combined conveniences which contribute to increased interest in Windows 10:
- It’s a free upgrade: Arguably one of the best features of Windows 10 is that it’s a free upgrade for one year following its release date. This gives enterprises the ability to thoroughly test its compatibility with software and other information systems, without deploying it throughout the entire infrastructure.
- The return of familiar features: Unlike Windows 8, which used a slick Metro-tiled user interface, Windows 10 brings back the traditional Start menu, making it feel more familiar than Windows 8.
- Less time spent on training staff: Organizations don’t have to train their staff as much on the various functions of Windows 10. Compared to Windows 8, which didn’t have the traditional Start menu or search bar, users don’t need nearly as much training to ensure they can function properly with the new operating system.
While Windows 10 is certainly an improvement over Windows 8, you don’t want to make the jump to a new operating system without first properly assessing your business’s needs. If you upgrade without checking your compatibility with certain legacy software, you could be left without access to your mission-critical applications. Doing so can lead to costly downtime that can have a direct impact on both your workers’ performance and your budget.
To avoid this, let Voyage Technology assist you with the upgrade process. We can provide a thorough assessment of your IT infrastructure, and break the process down so that you can understand what needs to happen before you make the shift to Windows 10. To learn more, give us a call at 800.618.9844.


