 The introduction of new and exciting technologies keeps changing the ways people interact. Innovations such as email, instant messaging, and the development of mobile devices are now turning out to be just fundamental steps to a more connected planet. The Internet of Things is set to turn human civilization on its head. What does this shift mean for the immediate future?
The introduction of new and exciting technologies keeps changing the ways people interact. Innovations such as email, instant messaging, and the development of mobile devices are now turning out to be just fundamental steps to a more connected planet. The Internet of Things is set to turn human civilization on its head. What does this shift mean for the immediate future?
Computers. Computers Everywhere!
Next time you are walking down the street, stop using your smartphone for a few minutes and watch all the people on the street with you. A good number of them, especially if they are alone, are doing what you were just doing, looking at their smartphone. With so many people tied to their devices, the demand for systems that integrate with these devices is at an all-time high.
While many people are excited to be able to utilize applications to do things they had to do manually just a short time ago, a much bigger change is on the horizon that seems to be something out of science fiction. Some of the greatest science fiction authors of the 20th century have been able to predict the shifts in the relationships that humans have with technology today.
Many of these stories are cautionary tales about not letting technology get too far out in front of humanity. So, what happens when nearly every item that people purchase can be connected to the Internet? It’s not too hard to see scenarios, in a world where everything, not just everyone, is connected can cause potential problems. The fact is that the current Internet of Things technological shift won’t be easy to get out from under if the technology comes off the assembly line as quickly as it seems to be.
Many consumer products are now beginning to be outfitted with what are known as “smart” capabilities. Basically, they can now be accessed from an outside remote, often an app that the user can access with a mobile device such as a smartphone. This shift in computing delivers the first major change toward computing omnipresence and integrates potentially millions of separate functions; resulting in a situation where computers easily outnumber users. As this happens, and as the Internet of Things begins to become evident for the end-user, manufacturers will certainly have to move quickly to integrate the devices they create with central points of control, or else face not having a market for their goods.
IoT and You
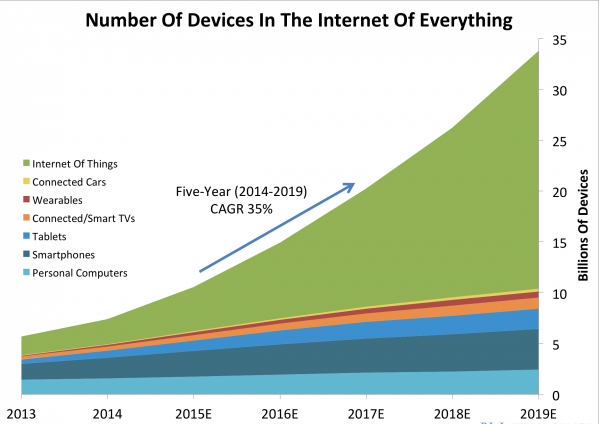
Manufacturers have used an element of market research, namely the drastic increased use of smartphone technology, to justify their expansion into the untested waters of the Internet of Things. In fact, there are plenty of numbers available to justify about any manufacturer of goods to take a look at the potential for profit in creating products that can be connected to the Internet. Cisco did the math and estimates that the Internet of Things creates a $19 trillion market. TechNavio states that over 17 billion “other” devices will be connected to the Internet by 2019; not counting smart TVs, wearable technology, smartphones, PCs, or even connected cars. As a result, the people at Gartner estimate that the services that will likely accompany these devices will come in well over their initial projections, likely exceeding $300 billion by 2020.
For this reason, manufacturers are already producing millions of connected goods, creating a market for goods that won’t take up a lot of bandwidth, but will make the user’s life easier. In these times, any time savings is worth a pretty penny on the open market. The World Economic Forum expects that by 2020, five billion people will have access to the Internet, which is sure to boost demand even further. In fact, the same publication suggests that there will be nearly 35 billion things connected to the Internet by the same year. Here is a graph representing that shift:
It seems as if the ubiquity of our computing systems is an inevitability. Here’s hoping that with computing becoming a growing aspect of humanity, that we, as a civilization, are smart enough to proceed in these untested waters with caution, and to avoid the major problems humans face in the science fiction worlds that were created so very long ago.
Do you think that the Internet of Things and the ubiquitous computing it brings will change change the world for the better? Do you think automation is a good thing or a bad thing for humanity? Share your thoughts in the comments.


