While the major holiday shopping days have passed us by, many people are still looking for that perfect gift often using the Internet to find it. While online shopping is certainly more convenient, it can also be dangerous. To help keep you safe this season and beyond, we’re reviewing a few practices to protect your identity while shopping online.
Stick to What You Know
There are a few reasons why it makes sense to stick to using well-known websites like Amazon while you conduct your holiday shopping. First of all, you likely already have an Amazon account, which means you can shop without creating another online account that could potentially be breached. In addition, a well-known site is more motivated to make things right if something does happen, as their higher status means that bad publicity could have a wider-reaching impact for them.
It’s hard to put a concrete value on trust, but even if a site is a little more pricey to shop on, the peace of mind that familiarity can bring is a powerful motivator.
Check the URL
Not all websites are as secure as others, so it pays to check that the website you’re browsing has a secure connection. An easy way to tell is to check the address bar in your browser. Most of today’s browsers will show a padlock there if your connection is secure.
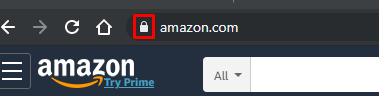
This lock signifies that the website you are visiting is using an SSL certificate, which essentially means that your connection to it is encrypted. Now, this doesn’t necessarily mean that the website is completely safe, but at least your connection to it is.
Use PayPal, Amazon Pay, or Apple Pay
Many websites offer you multiple options to submit a payment, including the traditional credit card route, or by using a third-party payment system (like PayPal, or other services that have popped up in recent years). These payment systems can help protect you from plugging your financial data into a website that you might not necessarily trust. Instead, when you use one of these services, the transaction goes through the service, while you are directed back to the store you were shopping on.
Avoid Scams and Phishing
Among all the holiday cheer, there can be a lot of stress as well, to the point that some people may sacrifice their cyber awareness, for the sake of just getting everything done. Cybercriminals use this to their advantage. If you receive an email that seems to offer something that’s just too good, it probably is - and don’t take any emails claiming there’s an issue with one of your accounts at face value. Instead, check the store’s website to confirm it. Most stores use email as a message board, broadcasting news to their customers so the customer can navigate to their website to interact further.
Holiday shopping can be much easier, thanks to the Internet, but that doesn’t mean that you can just assume that it’s safe. However, while you’re focused on getting the perfect gift for everyone on your list, we can help protect you and your business from holiday humbugs like cyberthreats. To learn more, give Voyage Technology a call at 800.618.9844.



